Top 4 Secured Smartphones in 2018
Privacy has been a major point of concern for smartphone users. Our phone is one of the best tracking devices available on the market today. Your smartphone primarily keeps pinging cell towers in your area/locality to make you a part of the cellular mobile network. The data connection then enables you to use different internet services from online cabs to watching movies.
All online service providers track cookies, advertising ids, and internet usage stats to enhance user experience and gather more insight into your likes and dislikes. Although internet companies use limited or capped user data after permission from the user itself, this is not the case when hackers gain access to your phone.
Smartphones despite some privacy issues are a necessity these days. However, a truly secure and private smartphone is a myth. Hence as buyers/users, we must be well informed about the privacy or security features of smartphones. In addition to this, Government Security Agencies all over the world now seek access to phone data of convicts or private individuals within government radar.
Moreover, smartphones are vulnerable to hacking exploits like KRACK and Blueborne. But with the plethora of smartphones flooding the market, selecting the best as per your security preference can be quiet tedious.In this blog, we try to select the best in the business from all the apparent evil options.
Following are the key security parameters for modern day smartphones.
Biometrics:
Biometric identifiers are unique. Unlike passwords, they can’t be changed or copied. However, if your biometric identifiers were ever stolen they cannot be replaced with new ones. It is equivalent to identity theft leaving you in a compromising position. However, the fact that biometric security eliminates human error like forgetting the password or even increases privacy from those constantly playing with your smartphone makes it a liability.
Encryption:
Encryption is paramount in today’s internet connected world. These smartphones support two kinds of encryption: File Based (FBE) or Full Disk (FDE). FBE scores over FDE in terms of security. All files in FBE have their own private key whereas in FDE all files are bundled together and they share one key for unlocking the entire data partition. The most secure of the smartphones use AES encryption standard, the keys used to decrypt the data can be 128-bit or 256-bit depending on the data value.
Hardware-Assisted Security:
iOS devises couple encryption with hardware assistance. However, the Android devices in our list use hardware as storage for cryptographic keys.
Sandboxed User Accounts:
The sandbox user account feature for Android devices allows users to separate available space on the device into two parts i.e. one for work, and another for personal usage. Sandbox completely separates user data from each other based on the desired categorization.
Restrict Ad Tracking:
iPhone and Android users are tracked using a system-wide advertising tracking ID. This ID remains attached to all services and apps you use on the phone.
Marketing partners of the phone use this tracking ID data to deliver targeted ads on your device. While iPhone users can filter/control an app’s ability to view and use this ID. Google on the other hand only allows users to reset the ID and completely opt out of seeing any related ads.
Always-On VPN:
VPN or Virtual Private Network allows data encryption for anonymity purpose. Android devices allow all kind of internet data to be passed via a VPN. This is not the case with iPhone. Apple allows VPN encryption only over Wi-Fi, unless and until user enables “ Supervised” mode to get the VPN working over mobile/carrier data.
Block Internet Access for Apps:
A local VPN setup like Netguard on your Android device can help you block or restrict internet access for specific apps on your mobile device. iOS users can simply disable their mobile data access for an app. But regulating wi-fi connectivity is not possible.
Data Wipe After Failed Login:
Brute-force password attacks are a comprehensive hacking method for breaking into your smartphone. The hackers use strong computational functions to generate a large number of combinations of your pin and password. The moment any of the randomly generated pins/password match, you stand to lose many things all at once.
This may include social security number, bank account, important contacts etc. Automatic factory reset option is one solution to this. If enabled, some phones undergo automatic reset the moment the intruders cross the threshold of allowed attempts.
OS CVEs:
Both iOS and Android phones are equally prone to common vulnerabilities and exposures (CVE’s) discovered. Hence we must keep a check on the exposure of these phones to CVEs.
All the top secure phones on our list either run on Android or iOS.
Security Patch Timeframe:
Timely security patches increase security. Security patches must be released on a timely basis. Updates are released within a month of critical bugs detection. Android sticks to consistent timeframes when releasing security updates. OEM is solely responsible for distribution of security updates provided by Google for Android.
Bug Bounties:
Smartphone manufacturers offer a good bounty to those enthusiasts who can find bugs as well weaknesses in phone’s software. Apple allows only trusted bug reporters to detect loopholes in security. Most other device makers let anybody report bugs and claim cash prizes. The higher the bounty, the higher the pool of crowd-sourced people involved in detecting possible security breaches.
Read Also: Best Waterproof Phones You Can Buy Today (IP67/68)
Factors That Made us Choose the Best Secure Smartphones
The phones in our list scored high on the key comparison points below than other smartphones.
- Inbuilt encryption.
- Granular Permission Management
- Remote lock and Wipe Capabilities.
- Hardware-Assisted Security: Apple uses a hardware encryption chip to strengthen security, while the Android OEMs here use some variation of a hardware root of trust system.
The phones in our list belong to a family of devices that deserved to be part of the list. These include original Google Pixel, Samsung’s Galaxy S8 lineup, Apple’s older iPhone 7 models.
1. BlackBerry KEYone
BlackBerry and privacy go hand in hand. Blackberry devices are ideal for both private and enterprise use. The new Blackberry KEYone which runs on Android OS coupled with the security features of the predecessors and TCL constructed hardware is the best smartphone
for the privacy-conscious user.
The safety features that make the phone impenetrable include:
Hardware Root of Trust: At each bootup, Cryptographic keys are injected into the processor to verify the device and to ensure no tampering occurred. Cryptographic keys during verification are scrambled immediately to combat attacks.
Stronger and Safer Kernel: Additional security patches to address vulnerabilities. Monthly Android security patches for two years.
Privacy Shade: A small view of the screen is visible rest all is rendered non-visible.Allowing very private user interaction with smartphone to negate any third party figuring out password from over your shoulders
DTEK: Monitors and checks apps that are sending your location or accessing your text messages. They immediately alert if anything fishy is detected.
Picture Password: A very different authentication process. Users hide a number in a secret location within a picture. To unlock, users must shift the secret number from a given grid to the location on the picture.
Full Disk Encryption: Unlike most Android devices BlackBerry ensures full-disk encryption.
Full-disk encryption secures everything on the hard drive (from your pictures to the root folder) via AES-128 encryption standard.
2. iPhone X
One thing that set apart Apple’s iPhone X from all other smartphone is its security. The reason for this is its operating system, the iOS. Due to its closed system, Apple can update all iOS devices at one go. Majority of Apple products are on the latest firmware, whereas less than one percent are running on the latest Android version.
Apple uses a much more refined model for file-based encryption. Some unique aspects of Apples file-based encryption are:
- Files and their metadata are encrypted separately using different keys.Another key based on user’s passcode and the hardware than encrypts these unique keys.
- Files are protected based on their content. Higher priority content is unlocked only if the device is on and unlocked. Other files require single authentication.
- Apple devices encounter a comparatively lower number of CVE’s (Common Vulnerabilities and Exposures). The closed ecosystem further ensures a malware less App Store.
Facial Recognition System: Apple’s face recognition system is both secure and intelligent.
Apples stores the user’s face map in a secure enclave. The secure enclave is an isolated piece of hardware.
Face Data sans some diagnostic data for apple support never leaves the user’s device. Apps which use Face ID for authentication have no access to the data and only receive alerts on successful authentication.
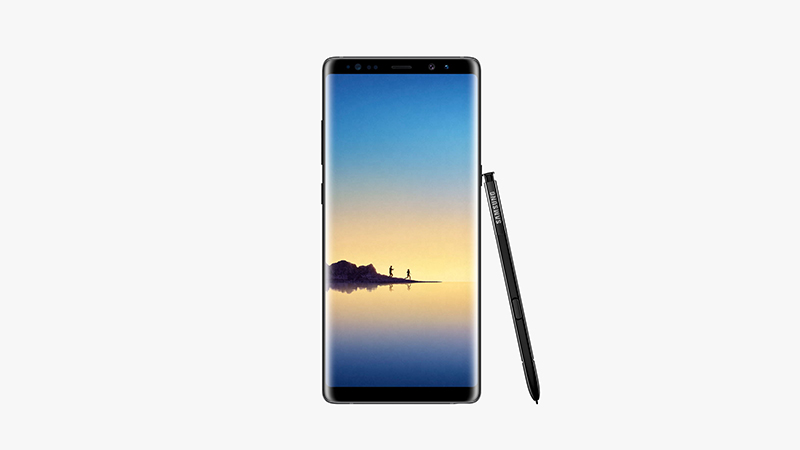
3. Galaxy Note 8
Samsung’s flagship offering comes with its own security platform known as Samsung Knox. The primary objective for KNOX is to ensure that there is an invisible secure wall between work environment and personal space of the user. It couples hardware and software together to provide deep-level security solutions and in the process isolate each environment effectively and securely. Rollback prevention further ensures regular firmware ant other patch updates.
Some of the key aspects of the Samsung Knox are:
Hardware Root of Trust: The unique inbuilt Device Root Key (a cryptographic key) is accessible in a secure environment known as the Trust Zone. This key is used to identify the device. Enterprise data are encrypted using this key.
Secure B: It checks and manages all components during the booting process. Secure Boot checks users from changing the bootloader or operating system of the device. However, it cannot prevent rooting.
The limitation of KNOX platform to prevent rooting brings it down to the third spot on our list.
4. Pixel 2 (Or Pixel 2 XL)
Last but not the least in our list is Google’s very own premium offering the Pixel 2 (and/or Pixel 2 XL). Though Google’s flagship model had a late patching of the KRACK vulnerability, it by no means makes it insecure. The hardware still makes it one of the most secure phones in the market.
Some security aspects that are worth special mention are:
Highly Protected Cryptographic keys: Authentication Process has had a transition from being software based to chip. This is physically separated from the SoC. The earlier authentication process trust zone was software based. Hence the new security module can prevent both software-based and physical attacks.
Regular patch and Firmware Updates: Google ensures/promises timely Android updates for three years on these phones. To protect your smartphone from any new threats, Google submits security patches without delay on a monthly basis.
Bug Bounty Programs: Google’s bug bounty programs are the best in the business.
Price money up to $200,000 for critical bugs is up for grabs. Hence, Pixel 2 enjoys a larger pool of bounty hunters as compared to other smartphones.
Conclusion
From the above list, we may conclude that for those who want thei] r phones and their data secure, the KEYone is the goto smartphone. Blackberry’s traditional enterprise-grade privacy and security outsmarts all and delivers the most secure and private phone. And if you are averse to an android based phone, iPhone X is the best iOS device for the users concerned with privacy.
Top 4 Secured Smartphones in 2018
http://www.blog.sagmart.com/wp-content/uploads/2018/02/best-secured-smartphones-in-2018-300x300.jpg Mobile and TabletTechnologyPrivacy has been a major point of concern for smartphone users. Our phone is one of the best tracking devices available on the market today. Your smartphone primarily keeps pinging cell towers in your area/locality to make you a part of the cellular mobile network. The data connection then enables you to use different internet services from online cabs to watching movies.
All online service providers track cookies, advertising ids, and internet usage stats to enhance user experience and gather more insight into your likes and dislikes. Although internet companies use limited or capped user data after permission from the user itself, this is not the case when hackers gain access to your phone.
Smartphones despite some privacy issues are a necessity these days. However, a truly secure and private smartphone is a myth. Hence as buyers/users, we must be well informed about the privacy or security features of smartphones. In addition to this, Government Security Agencies all over the world now seek access to phone data of convicts or private individuals within government radar.
Moreover, smartphones are vulnerable to hacking exploits like KRACK and Blueborne. But with the plethora of smartphones flooding the market, selecting the best as per your security preference can be quiet tedious.In this blog, we try to select the best in the business from all the apparent evil options.
Following are the key security parameters for modern day smartphones.
Biometrics:
Biometric identifiers are unique. Unlike passwords, they can’t be changed or copied. However, if your biometric identifiers were ever stolen they cannot be replaced with new ones. It is equivalent to identity theft leaving you in a compromising position. However, the fact that biometric security eliminates human error like forgetting the password or even increases privacy from those constantly playing with your smartphone makes it a liability.
Encryption:
Encryption is paramount in today’s internet connected world. These smartphones support two kinds of encryption: File Based (FBE) or Full Disk (FDE). FBE scores over FDE in terms of security. All files in FBE have their own private key whereas in FDE all files are bundled together and they share one key for unlocking the entire data partition. The most secure of the smartphones use AES encryption standard, the keys used to decrypt the data can be 128-bit or 256-bit depending on the data value.
Hardware-Assisted Security:
iOS devises couple encryption with hardware assistance. However, the Android devices in our list use hardware as storage for cryptographic keys.
Sandboxed User Accounts:
The sandbox user account feature for Android devices allows users to separate available space on the device into two parts i.e. one for work, and another for personal usage. Sandbox completely separates user data from each other based on the desired categorization.
Restrict Ad Tracking:
iPhone and Android users are tracked using a system-wide advertising tracking ID. This ID remains attached to all services and apps you use on the phone.
Marketing partners of the phone use this tracking ID data to deliver targeted ads on your device. While iPhone users can filter/control an app’s ability to view and use this ID. Google on the other hand only allows users to reset the ID and completely opt out of seeing any related ads.
Always-On VPN:
VPN or Virtual Private Network allows data encryption for anonymity purpose. Android devices allow all kind of internet data to be passed via a VPN. This is not the case with iPhone. Apple allows VPN encryption only over Wi-Fi, unless and until user enables “ Supervised” mode to get the VPN working over mobile/carrier data.
Block Internet Access for Apps:
A local VPN setup like Netguard on your Android device can help you block or restrict internet access for specific apps on your mobile device. iOS users can simply disable their mobile data access for an app. But regulating wi-fi connectivity is not possible.
Data Wipe After Failed Login:
Brute-force password attacks are a comprehensive hacking method for breaking into your smartphone. The hackers use strong computational functions to generate a large number of combinations of your pin and password. The moment any of the randomly generated pins/password match, you stand to lose many things all at once.
This may include social security number, bank account, important contacts etc. Automatic factory reset option is one solution to this. If enabled, some phones undergo automatic reset the moment the intruders cross the threshold of allowed attempts.
OS CVEs:
Both iOS and Android phones are equally prone to common vulnerabilities and exposures (CVE’s) discovered. Hence we must keep a check on the exposure of these phones to CVEs.
All the top secure phones on our list either run on Android or iOS.
Security Patch Timeframe:
Timely security patches increase security. Security patches must be released on a timely basis. Updates are released within a month of critical bugs detection. Android sticks to consistent timeframes when releasing security updates. OEM is solely responsible for distribution of security updates provided by Google for Android.
Bug Bounties:
Smartphone manufacturers offer a good bounty to those enthusiasts who can find bugs as well weaknesses in phone’s software. Apple allows only trusted bug reporters to detect loopholes in security. Most other device makers let anybody report bugs and claim cash prizes. The higher the bounty, the higher the pool of crowd-sourced people involved in detecting possible security breaches.
Read Also: Best Waterproof Phones You Can Buy Today (IP67/68)
Factors That Made us Choose the Best Secure Smartphones
The phones in our list scored high on the key comparison points below than other smartphones.
- Inbuilt encryption.
- Granular Permission Management
- Remote lock and Wipe Capabilities.
- Hardware-Assisted Security: Apple uses a hardware encryption chip to strengthen security, while the Android OEMs here use some variation of a hardware root of trust system.
The phones in our list belong to a family of devices that deserved to be part of the list. These include original Google Pixel, Samsung’s Galaxy S8 lineup, Apple’s older iPhone 7 models.
1. BlackBerry KEYone
BlackBerry and privacy go hand in hand. Blackberry devices are ideal for both private and enterprise use. The new Blackberry KEYone which runs on Android OS coupled with the security features of the predecessors and TCL constructed hardware is the best smartphone
for the privacy-conscious user.
The safety features that make the phone impenetrable include:
Hardware Root of Trust: At each bootup, Cryptographic keys are injected into the processor to verify the device and to ensure no tampering occurred. Cryptographic keys during verification are scrambled immediately to combat attacks.
Stronger and Safer Kernel: Additional security patches to address vulnerabilities. Monthly Android security patches for two years.
Privacy Shade: A small view of the screen is visible rest all is rendered non-visible.Allowing very private user interaction with smartphone to negate any third party figuring out password from over your shoulders
DTEK: Monitors and checks apps that are sending your location or accessing your text messages. They immediately alert if anything fishy is detected.
Picture Password: A very different authentication process. Users hide a number in a secret location within a picture. To unlock, users must shift the secret number from a given grid to the location on the picture.
Full Disk Encryption: Unlike most Android devices BlackBerry ensures full-disk encryption.
Full-disk encryption secures everything on the hard drive (from your pictures to the root folder) via AES-128 encryption standard.
2. iPhone X
One thing that set apart Apple’s iPhone X from all other smartphone is its security. The reason for this is its operating system, the iOS. Due to its closed system, Apple can update all iOS devices at one go. Majority of Apple products are on the latest firmware, whereas less than one percent are running on the latest Android version.
Apple uses a much more refined model for file-based encryption. Some unique aspects of Apples file-based encryption are:
- Files and their metadata are encrypted separately using different keys.Another key based on user’s passcode and the hardware than encrypts these unique keys.
- Files are protected based on their content. Higher priority content is unlocked only if the device is on and unlocked. Other files require single authentication.
- Apple devices encounter a comparatively lower number of CVE’s (Common Vulnerabilities and Exposures). The closed ecosystem further ensures a malware less App Store.
Facial Recognition System: Apple’s face recognition system is both secure and intelligent.
Apples stores the user’s face map in a secure enclave. The secure enclave is an isolated piece of hardware.
Face Data sans some diagnostic data for apple support never leaves the user’s device. Apps which use Face ID for authentication have no access to the data and only receive alerts on successful authentication.
3. Galaxy Note 8
Samsung’s flagship offering comes with its own security platform known as Samsung Knox. The primary objective for KNOX is to ensure that there is an invisible secure wall between work environment and personal space of the user. It couples hardware and software together to provide deep-level security solutions and in the process isolate each environment effectively and securely. Rollback prevention further ensures regular firmware ant other patch updates.
Some of the key aspects of the Samsung Knox are:
Hardware Root of Trust: The unique inbuilt Device Root Key (a cryptographic key) is accessible in a secure environment known as the Trust Zone. This key is used to identify the device. Enterprise data are encrypted using this key.
Secure B: It checks and manages all components during the booting process. Secure Boot checks users from changing the bootloader or operating system of the device. However, it cannot prevent rooting.
The limitation of KNOX platform to prevent rooting brings it down to the third spot on our list.
4. Pixel 2 (Or Pixel 2 XL)
Last but not the least in our list is Google’s very own premium offering the Pixel 2 (and/or Pixel 2 XL). Though Google’s flagship model had a late patching of the KRACK vulnerability, it by no means makes it insecure. The hardware still makes it one of the most secure phones in the market.
Some security aspects that are worth special mention are:
Highly Protected Cryptographic keys: Authentication Process has had a transition from being software based to chip. This is physically separated from the SoC. The earlier authentication process trust zone was software based. Hence the new security module can prevent both software-based and physical attacks.
Regular patch and Firmware Updates: Google ensures/promises timely Android updates for three years on these phones. To protect your smartphone from any new threats, Google submits security patches without delay on a monthly basis.
Bug Bounty Programs: Google’s bug bounty programs are the best in the business.
Price money up to $200,000 for critical bugs is up for grabs. Hence, Pixel 2 enjoys a larger pool of bounty hunters as compared to other smartphones.
Conclusion
From the above list, we may conclude that for those who want thei] r phones and their data secure, the KEYone is the goto smartphone. Blackberry’s traditional enterprise-grade privacy and security outsmarts all and delivers the most secure and private phone. And if you are averse to an android based phone, iPhone X is the best iOS device for the users concerned with privacy.




Leave a Reply